CVE-2026-31431
“Copy Fail” A Small Optimization, A Massive Linux Kernel Risk

DESCRIPTION
What started as a performance optimization in the Linux kernel has turned into a widespread security issue affecting millions of systems worldwide.
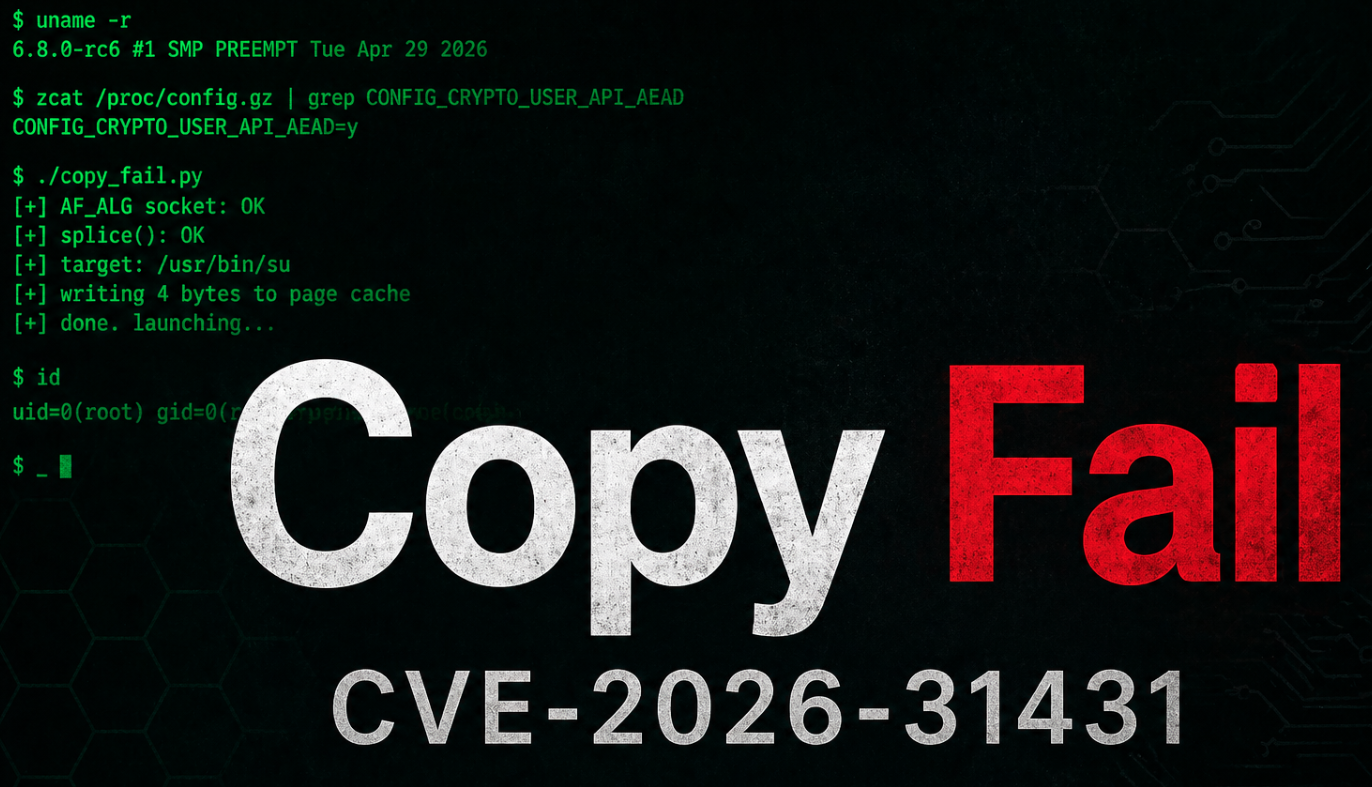
CVE-2026-31431, also known as “Copy Fail,” is a logic flaw in the Linux kernel’s AF_ALG userspace cryptography interface, specifically within the algif_aead and authencesn modules. The vulnerability was disclosed by researchers from Theori, who also released a dedicated project page and a working exploit.
At its core, the issue stems from a 2017 in-place optimization that allowed user-controlled data to be written into a writable page-cache-backed scatterlist. While intended to improve performance, this change introduced a dangerous assumption about data safety.
By chaining an AF_ALG socket with the Linux splice() system call, an unprivileged local attacker can achieve a deterministic 4-byte write primitive into the page cache of any readable file.
This includes highly sensitive binaries such as /usr/bin/su.
With careful manipulation, an attacker can modify critical instructions in memory redirecting execution flow (for example, forcing a different syscall). The result: executing su yields a root shell.
Even more striking, the publicly released exploit is extremely compact—reportedly fitting within 732 bytes of Python code making exploitation both practical and accessible.
AFFECTED SYSTEMS
This vulnerability has an unusually broad impact due to its long-standing presence:
• All Linux kernels from July 2017 to April 2026
• Major distributions, including:
Red Hat, AlmaLinux, Rocky Linux, CentOS, Ubuntu, Debian, SUSE, CloudLinux
• Cloud environments, container hosts, and CI/CD runners
• Multi-user systems such as shared hosting platforms
In short: almost every modern Linux system from the past eight years is potentially affected.
VULNERABILITY IMPACT
CVE-2026-31431 is classified as a Local Privilege Escalation (LPE) vulnerability but its real-world impact is far from limited.
An attacker who already has access to a system (even as a low-privileged user) can:
• Perform controlled memory modifications in the page cache
• Tamper with critical system binaries (e.g., /usr/bin/su)
• Escalate privileges to root
• Break container isolation boundaries in shared environments
Although exploitation requires local access, this condition is often trivial in real-world scenarios such as:
• Shared servers
• Compromised web applications
• Developer or CI environments
This makes “Copy Fail” particularly dangerous in modern infrastructure.
RECOMMENDATIONS
Immediate action is strongly advised:
1. Apply Kernel Updates
• Update to a patched kernel version released after April 2026.
2. Reboot Systems
• A reboot is required to fully apply kernel fixes.
3. Use Live Patching (if available)
• Solutions like KernelCare can mitigate the issue without downtime.
4. Restrict Local Access
• Limit shell access and reduce exposure in shared environments.
5. Monitor for Abuse
Watch for unusual behavior involving:
• AF_ALG sockets
• abnormal splice() usage
• unexpected execution of privileged binaries
TIMELINE
• July 2017 – Vulnerable optimization introduced into the Linux kernel
• April 1, 2026 – Fix committed to mainline (optimization reverted)
• April 22, 2026 – CVE shared privately with vendors
• April 29, 2026 – Public disclosure via oss-security; exploit released publicly
• April 30, 2026 – Livepatch solutions begin rolling out